4 minutes
Plus, five tips to avoid falling prey to malware and phishing at your credit union
According to a whitepaper from Sophos, 70% of internet users use the same password for almost all the web services they use. So it comes as no surprise that phishing is such a popular and effective tool for cyber criminals, allowing them to assume control of all types of accounts for a single victim, from social media to online banking.
Phishing is a type of cybercrime that involves deceiving users into thinking they are communicating with a legitimate company or individual, perhaps within their own organization, in order to steal confidential information and passwords. By its nature, a phishing attack works by impersonating someone the recipient knows and trusts, often by email or online messaging through social networks.
For insight into threats focused on specific people, cybersecurity company Proofpoint Inc., Sunnyvale, California, examined the most highly targeted attacks against Fortune Global 500 customers between July and September 2018, collecting the most-targeted email addresses for each company. Proofpoint then found the recipients’ titles and functions using social media profiles, internet databases, public records, news stories and other sources.
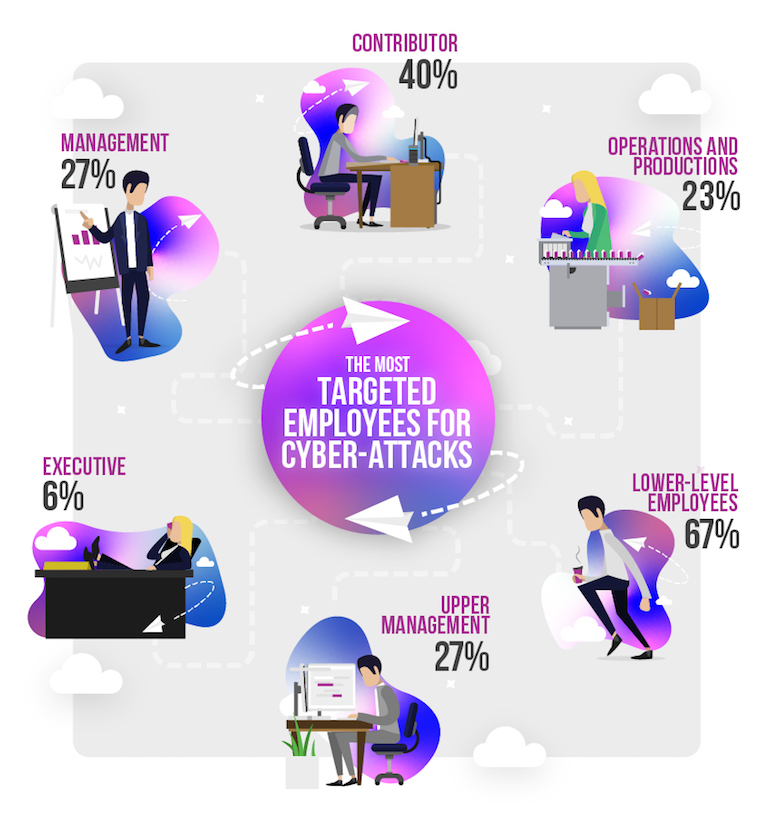
The Proofpoint report notes that “individual contributors and lower-level management” were subject to 67% of highly targeted—or spear phishing—attacks. While employees in the production and operations functional areas represented 23% of attacks, targeting of users in marketing, public relations and human resources is on the rise, together accounting for almost 20% of all phishing and malware attacks.
However, given that fewer users total fall into the upper management category, the report suggests that those in C-level positions, directors and department managers may be targeted disproportionately more often. Management and upper management are both targeted by 27% of phishing attacks within surveyed organizations, and executives receive approximately 6% of the most highly targeted emails.
Interestingly, when considering which industries are most targeted by email fraud, pharmaceutical drug manufacturers came out on top with 71 highly targeted attacks per company on average over a period of three months, according to the report.
While financial services didn’t crack the Proofpoint list of top targeted industries, the sheer quantity of sensitive data collected by these organizations, including credit unions, means they could be attractive targets. As such, Reboot Digital Marketing Agency has gathered five top tips for avoiding malware and phishing scams at work:
1. Know What to Look For
Pay close attention to attachments, advertisements and pop-up alerts, ensuring you only open what you trust. Train users to spot malicious emails and websites by teaching them what to look out for. Hackers are capable of spoofing email addresses you would normally trust, so be sure the contents of the email look legitimate before acting on instructions or opening attachments.
2. Avoid Unsolicited Links and Attachments
Most of the time, you should know the sender of an email and trust the source it is coming from before opening it. If unsure, go with the assumption that it is best to avoid opening attachments from an unknown source/sender altogether. Although a lot of companies employ malware scanning features, you shouldn’t rely solely on technology to protect you.
3. Turn Off HTML in Emails
HTML in emails can sometimes allow malware scripts to run once the email has been opened. For this reason, you might consider disabling HTML in your email client to lower the risk of an attack.
4. Scan External Drives for Threats
USB and external hard drives can contain malware that, if connected to a device on your organization’s network, can spread across the workplace onto other computers. To be extra vigilant, scan all external devices with antivirus software each time you connect one to a computer.
5. Regularly Change Your Password
Though this may seem obvious, it is easy to forget to regularly update your passwords—and it’s common to be reluctant to do so in fear of forgetting them. However, for security purposes, it is good practice to change your passwords every 90 days.
Following these security best practices can help keep your organization’s data safe—even if the CU industry earns the unfortunate distinction of being a top target in the future.
Shai Aharony is the proud founder and managing director of Reboot Digital Marketing, London, a fresh and innovative digital marketing company built on the most important and rarest of foundations: amazing people. Aharony regularly contributes his time and knowledge researching innovative and newsworthy articles for online communities.





